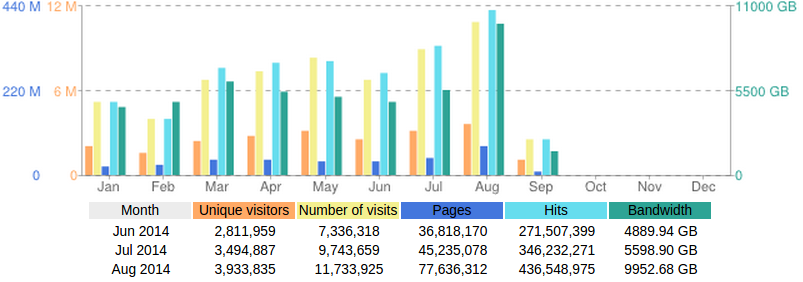
 Ongoing conflicts in Ukraine and the Middle East saw a stream of independent media and human rights organizations turn to Deflect for DDoS protection. The network delivered over 75 million pages to legitimate readers in August, our highest numbers to date. One week in particular stood out as we brought on-board two websites in the midst of ongoing DDoS attacks against them.
Ongoing conflicts in Ukraine and the Middle East saw a stream of independent media and human rights organizations turn to Deflect for DDoS protection. The network delivered over 75 million pages to legitimate readers in August, our highest numbers to date. One week in particular stood out as we brought on-board two websites in the midst of ongoing DDoS attacks against them.
One of the sites was getting hit by a botnet built on a newer version of the Dirt Jumper malware. We had previously trained our edges to recognize and protect against Dirt Jumper bots but this network displayed different behaviour to which we had to adapt. Their attacks did not bypass our caching network.
The other site came on board in the midst of a sophisticated and prolonged attack using various methods to bring them down. One notable vector of attack was using a Pingback DDoS from infected hosts running WordPress software. This is a type of reflection attack exploiting WordPress code built-in to the core package to improve a website’s SEO rankings. Furthermore, attackers were using their entire 14,000 hosts network in concert and hitting the target from each bot once or twice at a time. This is unusual behaviour as botnets usually try to overwhelm the website by hitting it often and hard (thereby giving away their malicious intention). In this particular case, the botnet was tailored to attack targets behind a caching infrastructure such as ours. Initial pattern recognition was difficult for the IPs in question. The sysops team quickly caught up though and isolated all hosts from accessing the network. Herein an example of a log entry from this attack.
SOURCE_IP – [DATE_AND_TIME] “GET /PAGE HTTP/1.0” http SITE_DOMAIN 200 158580 “WordPress/3.9.2; http://ATTACKERWORDPRESS; verifying pingback from PINGBACKURL” TCP_MISS text/html ORIGIN_SERVER 5621
Readers running websites on WordPress software are advised to install the Disable XML-RPC Pingback plugin to prevent their instance being abused by this attack.
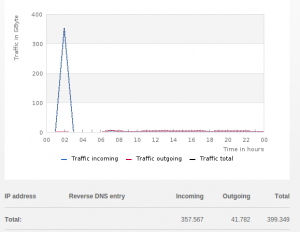
Due to the nature of our infrastructure we do not see lower network level DDoS traffic – relying on numerous providers around the world hosting our caching servers to absorb them. This makes it difficult for us to judge precisely the size of an attack. In such cases we rely on our providers’ statistics and emails warning us about huge traffic loads. Between August 7-8 simultaneous attacks against Deflect clients generated traffic levels somewhere in-between 8 to 10 Gbps.
Both websites were initially protected by Cloudflare. One organization was even paying the 200USD per month account fee promising advanced DDoS mitigation. Deflect’s mandate is to protect and enable online voices for qualifying independent media and human rights organizations and operate on a strict policy to never deny or terminate a service simply for being the target of a large attack.
We do not usually disclose our clients to the public. This time we sought their permission, as we believe our service and principles are exemplified by standing up for an organization that defends the human rights of all, even when it is against popular opinion in their own country. B’Tselem, the Israeli Information Center for Human Rights in the Occupied Territories, monitors and documents human rights abuses, conducts research into human rights issues, promotes accountability for human rights abuses and media, advocacy and public education.
As an organization dedicated to safeguarding human rights in the occupied West Bank and Gaza Strip, we have faced many attempts to silence our voice. During the latest fighting in the Gaza Strip, attempts by opponents of free speech escalated, including stepped-up DDoS attacks which our previous hosting providers failed to repel. Deflect proved itself extremely helpful in protecting our website, and has allowed us to carry on with getting our information out to the public here in Israel, Palestine, and abroad.
– Hagai El Ad, Executive Director, B’Tselem
B’Tselem is a winner of the 2014 Stockholm Human Rights Award and nominee for this year’s Václav Havel Human Rights Prize.